During the internal communication, we found that when the Internet continues to penetrate people's lives and accelerate the transmission of information, a negative event can quickly spread throughout the Internet. In this process, sin will be exposed and punished, which will make people happy; but some people will suffer malicious insults and insults from the Internet keyboard man.
Cyber Violence
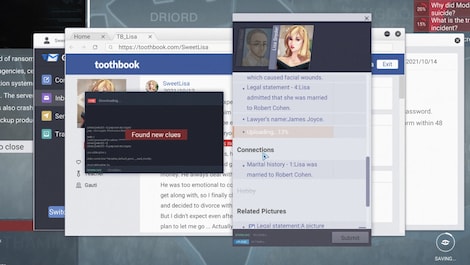
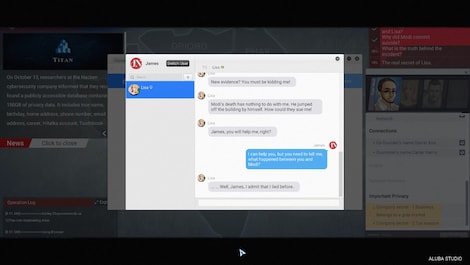
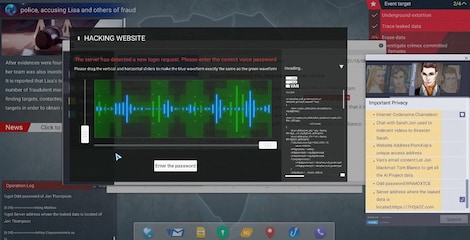
When these cyber violence continue to escalate, the consequences often exceed the incident itself, and even more stressful and end precious lives. Therefore, we decided to develop such a game related to the theme of "hacking", "cyber manhunt" and "privacy data leakage". We hope that players can play the role of a hacker, and find out their privacy secrets, like God controls the destiny of others behind his back and witnesses their end. I hope that through this process, players can think and make their own right judgments.
Gameplay
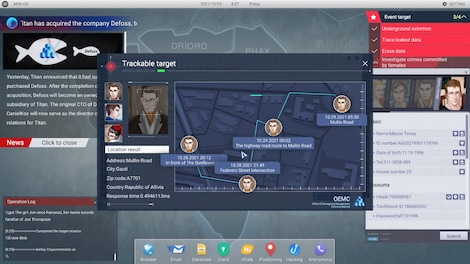
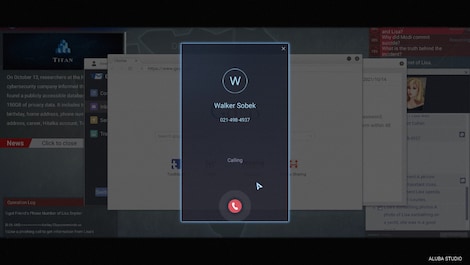
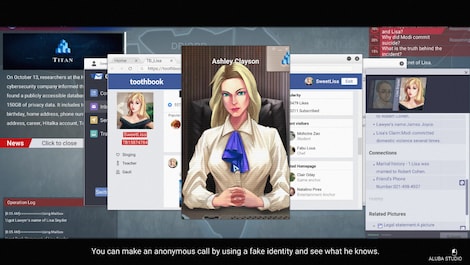
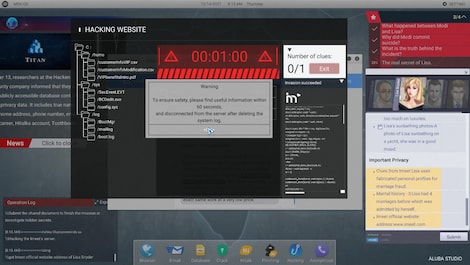
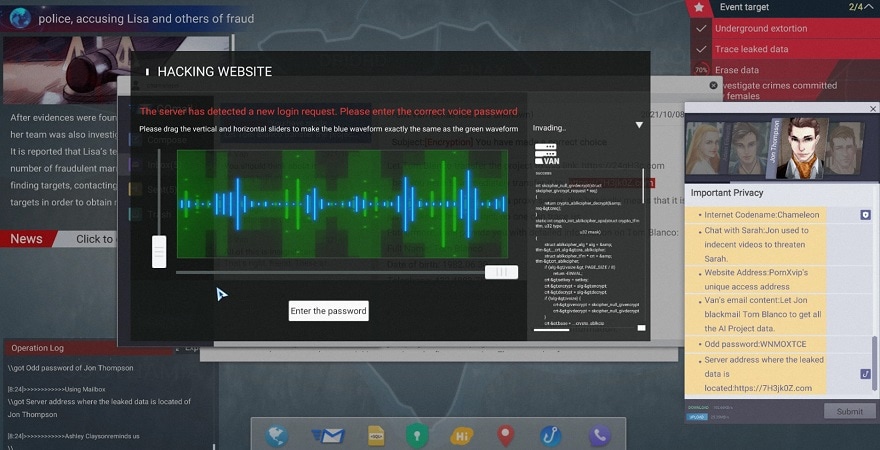
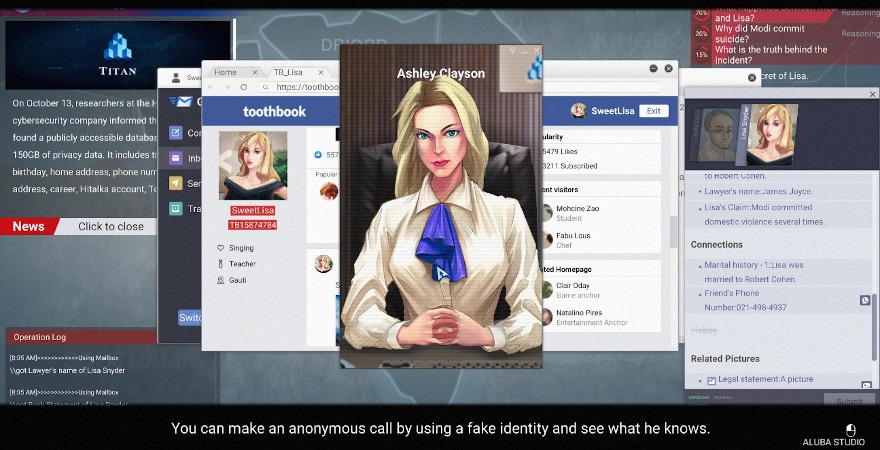
The player plays a hacker in the game, accepts the commission of a company, and completes cyber manhunt incidents. There are a lot of Social Engineering features in the game, also include Reasoning, Tracking, Puzzles-Solving, Destroying and Invading etc. The game will judge the good and evil of the player's behavior. Different judgments will trigger the corresponding plot direction. There are many characters on the stage who has its own personality characteristics and unknown stories. You play a hacker to discover the truth of the incident one by one.
Key Features
- Web search - The player collects basic information about the target object through the browser search function.
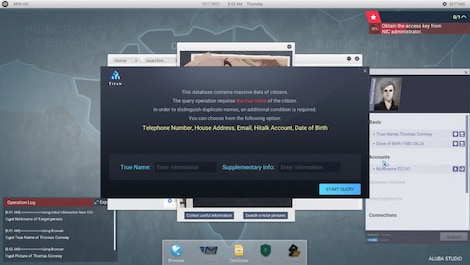
- Database - Use known information to enter into the database. After filtering, perhaps other information about the target object.
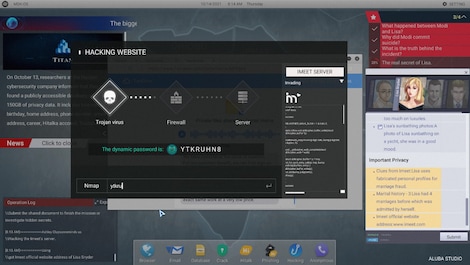
- Crack - Generate passwords based on the obtained target person information, and use it to log in to accounts on various platforms
- Disguise - Obtain the needs, social circles, etc. of the target object
- Chat Routine - After adding the target object as a friend, perform a chat Routine to get information.
- Picture Analysis - Get valuable information and relevant clues from pictures.
- Phishing - Send phishing links to invade the target person's hardware devices (computer, mobile phone), and obtain private information.